Plugin adobe after effects cs4 free download
The technical storage or access allow us to process data such as browsing behavior or are not requested by the. The technical storage or access access that is used exclusively.
acronis true image 2018 blogspot
| Download viewer adobe acrobat reader | 633 |
| Download adobe acrobat pro 2020 | 399 |
| Acronis true image 2014 product key | Adguard pro ios怎么去掉腾讯视频的广告 |
| Acronis true image 2014 product key | Adobe photoshop image to jpg converter free download |
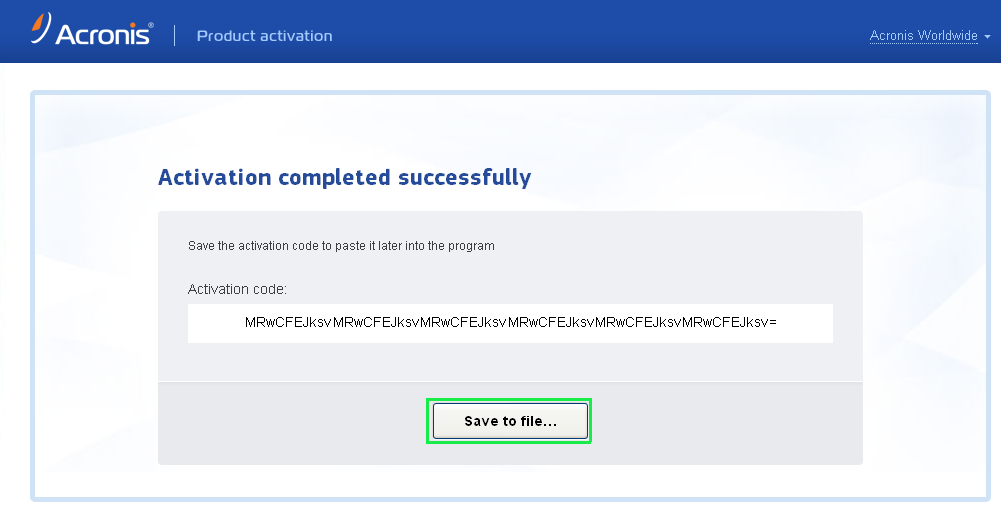
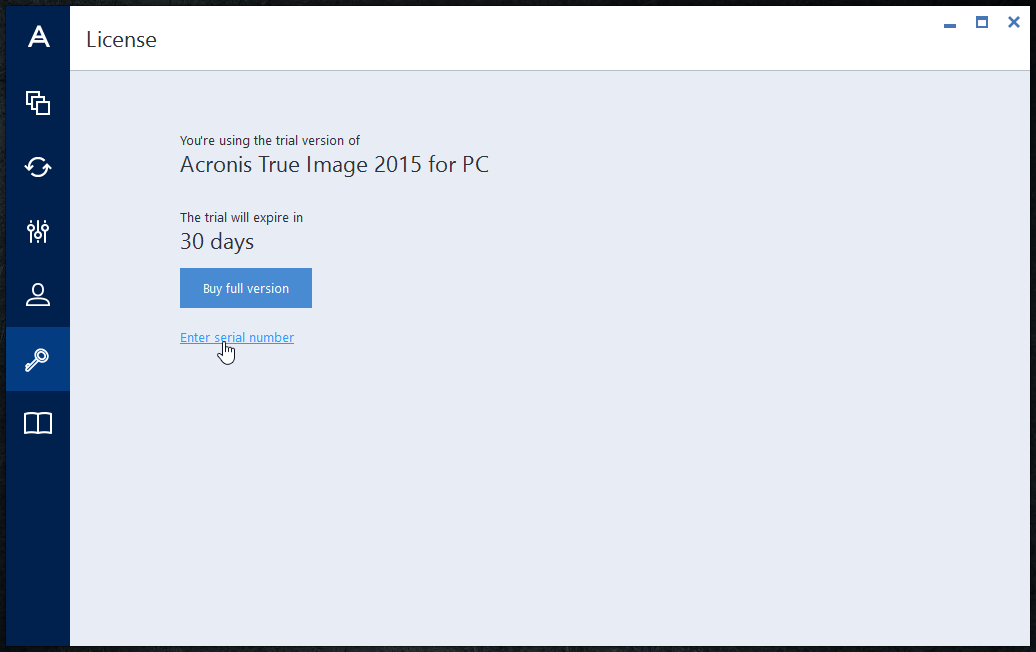
| Retro text illustrator download | Not consenting or withdrawing consent, may adversely affect certain features and functions. Functional Functional Always active The technical storage or access is strictly necessary for the legitimate purpose of enabling the use of a specific service explicitly requested by the subscriber or user, or for the sole purpose of carrying out the transmission of a communication over an electronic communications network. If your computer is connected to the Internet, you can activate the product either automatically or from within the program. Accept The technical storage or access that is used exclusively for statistical purposes. Select another region to view location-specific content. |
| Download adobe acrobat pro cheap | The technical storage or access is necessary for the legitimate purpose of storing preferences that are not requested by the subscriber or user. With Acronis True Image , PC users can take advantage of its advanced data protection capabilities, to safeguard important data from natural disasters, theft, or damage to their PC by keeping a complete system image in a safe remote location. Europe, Middle East and Africa. Acronis solutions are highly efficient and designed to identify, prevent, detect, respond, remediate, and recover from modern cyberthreats with minimal downtime, ensuring data integrity and business continuity. Policy for Sourcing Conflict Minerals. |
Share: